What if I told you the world wide web was overrun with zombies, hostile bots and sleeper cells? No this isn’t the plot of a new sci-fi flick; this is real life. And the threats are lurking right behind your computer screen.
Hackers and cybercriminals are recruiting internet-connected devices through spam emails and malware downloads. Once infected, the ‘bot’ or ‘zombie’ device will obey the commands of the remote hacker to, say, propagate spam emails to your coworkers and family members.
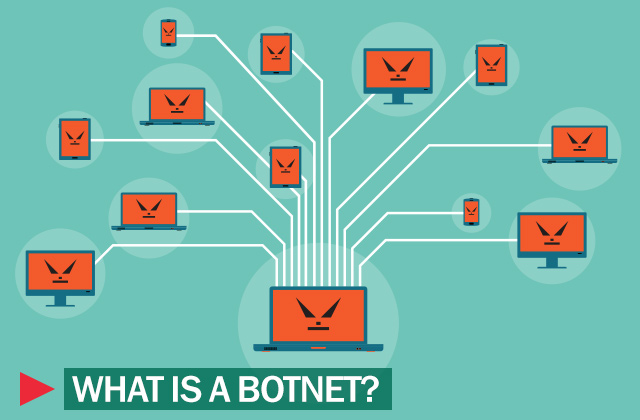
Once a hacker recruits enough devices, they have what is known as a botnet, a cyber weapon that can greatly increase the amount of damage the hacker is capable of inflicting to your network. And since malware can covertly exist inside your machine, you probably wouldn’t even know if your computer or mobile device was working for a hacker right now!
Amassing a zombie army is easier than you’d imagine. While the majority of devices are infected by malware downloads and spam emails (as mentioned above), devices can also be compromised through automated attacks.
Take for example the Mirai botnet, which is composed of compromised Internet of Things devices (like webcams, Wi-Fi routers, DVRs and baby monitors). Savvy hackers have found a way to infiltrate these devices by using a list of default security credentials.
Similarly, cybercriminals can crack passwords with automated brute force attacks, which basically guess what your password could be thousands of times until access is achieved.
Technology experts predict there will be between 20 to 30 billion IoT-enabled device by the year 2020; and since these devices are notorious vulnerable to hacking (and because hackers can scan the entire internet for exposed servers with open ports), we can expect larger, more disruptive botnet attacks in the future.
This is frightening news considering that 2016 was rocked by some of the largest DDoS attacks in history. In October, Mirai botnet was used to crash Dyn, a popular DNS provider to some of the world’s top companies like Amazon, Netflix, Spotify and Twitter. But even that massive attack looks like it could be dwarfed by the capabilities of the Leet Botnet.
Of course, botnets aren’t only useful for DDoS attacks. They can also be used to distribute malware, run phishing campaigns, extort businesses and launder stolen money.
In November 2016, international law enforcement agencies took down Avalanche, one of the largest active cybercrime syndicates in the world. According to the Department of Justice, this cybercrime ring is allegedly responsible for hundreds of millions of dollars in global monetary losses and more than two dozen malware families plaguing the internet.
While this takedown is good news for the world wide web, it is hardly an end to the blight of global cybercrime. All hope is not lost, however. There are still steps you can take to prevent a botnet attack and protect your business.
Prevention
To prevent a botnet attack from crippling your business operations, consider investing in DDoS mitigation techniques, such as ‘blackholing’ or ‘sinkholing.’ These methods redirect harmful traffic to a null interface or non-existent server to inhibit any real damage the hacker could inflict. Similarly, upstream filtering detects and scrubs bad traffic from reaching your servers before allowing good traffic to reach your site.
You can also prevent a botnet attack from taking over your computer or internet-connected device by ignoring spam emails, clickbait and illegitimate web downloads. If you buy a new device or router, be sure to change the security credentials immediately. After all, it only takes a few minutes for cyber crooks to discover and recruit your favorite machines.
Finally, if you believe your device has been infected by malware (or are simply paranoid after reading this article), talk with your IT team or cybersecurity provider to root out any malicious programs or suspicious software from your network.
Don’t let your business fall prey to the zombie horde, safeguard your organization today!







